Starting in August 2019, MIT was being put on the spot for accepting money from Jeffrey Epstein and accusations against the late Marvin Minsky for having sex with one of his victims resurfaced. In a call for protest, someone even wrote that Marvin Minsky assaulted her. In reaction Richard Stallman replied in an email that “the word “assaulting” presumes that [Marvin Minsky] applied force or violence, in some unspecified way, but the article itself says no such thing”. The rise of the “cancel culture” makes it very hazardous to publicly say or write anything regarding sexism, prostitution or racism. Despite this, Richard Stallman has published a number of blog entries on those topics over the years, ignoring people urging him to stop or become a target. But this time he caught the attention of someone.
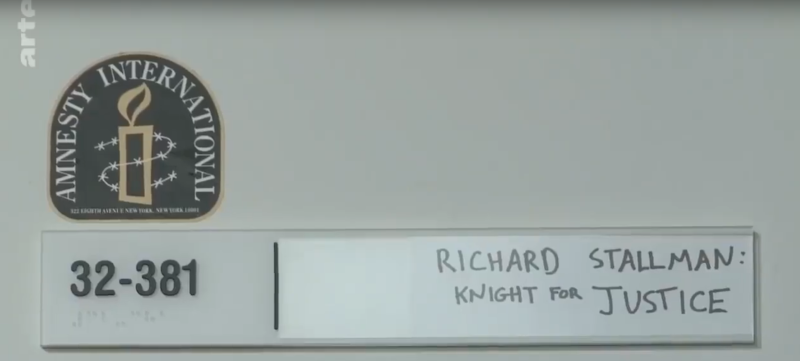
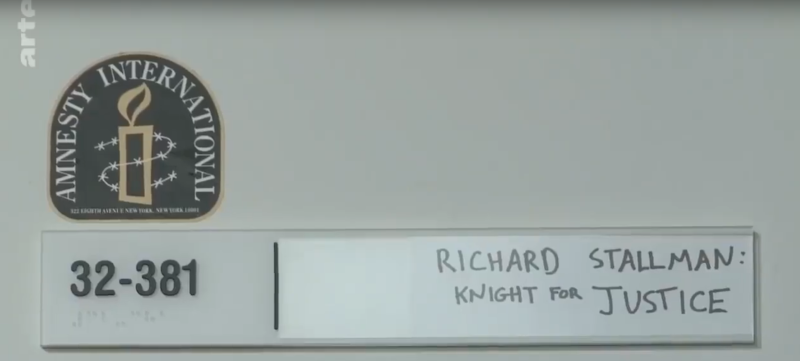
After reading Richard Stallman email, Selam G. published an article and commented: “[Richard Stallman] says that an enslaved child could, somehow, be “entirely willing””. What Richard Stallman actually wrote is: “We can imagine many scenarios, but the most plausible scenario is that she presented herself to him as entirely willing. Assuming she was being coerced by Epstein, he would have had every reason to tell her to conceal that from most of his associates”. More tabloid articles followed, further mischaracterising Richard Stallman statements. A photo of Richard Stallman office door at MIT labeled “Richard Stallman: Knight for Justice (also: hot ladies)” was also included in Selam G.’s article as a proof against Richard Stallman.
In response, Richard Stallman commented on his blog: “headlines say that I defended Epstein. Nothing could be further from the truth. I’ve called him a “serial rapist”, and said he deserved to be imprisoned.” As for the label on Richard Stallman office door, it was added by an unknown person, over a decade ago. In a documentary shot in 2017/2018, it only reads “Richard Stallman: Knight for Justice” (at 6:22) because Richard Stallman removed the ending: (also: hot ladies). The content and the tone of Selam G.’s article is archetypal of the cancel culture and she was joined by people sharing the same faith to demand the resignation of Richard Stallman.
Any effort to establish the truth was a loss of time: Richard Stallman participating in a discussion about rape and prostitution was blasphemy. He was not attacked for what he wrote, he was attacked for writing on a forbidden topic. Another similar and well documented instance is what happened to Bret W. in 2017 at the Evergreen College when he wrote “one’s right to speak –or to be– must never be based on skin color” in an email. In both cases there were many witness who did not intervene for fear of being the next target. I also stayed silent and horrified while Richard Stallman was shamed publicly. I wanted to believe it would blow over after a few days. I trusted the Free Software community to be rational and eventually disregard this episode. I was sorely mistaken.
Two days after Selam G. article was published, Software Freedom Conservancy who is run by some of the most influential people in the Free Software movement, published a statement demanding Richard Stallman’s resignation from the FSF. Neil McGovern, executive director of GNOME, also asked for Richard Stallman resignation and links to a tabloid article grossly mischaracterising Richard Stallman. They endorsed the attacks and legitimized them in the eye of the Free Software community. The next day Richard Stallman resigned from his position as president of the FSF.
It all happened very quickly but the roots of Richard Stallman’s dispute with other members of the Free Software community are deep. Software Freedom Conservancy states that “when considered with other reprehensible comments [Richard Stallman] has published over the years, these incidents form a pattern of behavior that is incompatible with the goals of the free software movement” and Neil McGovern wrote something similar. Although they did not reference any specific event, there are some publicly available records of past disputes. For instance, in September 2018, Richard Stallman wrote a blog entry very similar to the defense of Marvin Minsky. He rewrote it in the following weeks because, in his own words: “some people reading earlier versions of this note seem to have got the idea that I condone enslavement of prostitutes”.
I can only assume the respected members of the Free Software community who leveraged the cancel culture and tabloid journalism felt justified because of years of frustrating disputes with Richard Stallman. But they made a terrible mistake. Richard Stallman was unjustly and severely punished. He no longer has a position at the FSF, which he founded 34 years ago, he also lost his position at MIT, his scheduled talks could be canceled and he lost his home.
History will remember that in 2019 Richard Stallman took a major hit from the cancel culture and tabloid journalists. And also that respected members of the Free Software community endorsed the cancel culture and tabloid journalists. They sent an ominous message to all their opponents: we fight dirty. They negated the benefit of dialog, any sense of rational thinking and threw away years of debate with Richard Stallman. Leveraging someone who had no clue about the past disputes to get rid of their opponent proved to be much more efficient. We should now expect that some Free Software activists will use the cancel culture as a mean to an end. But what they should do instead is to ignore the furor, wait until it passes and resume a discussion based on truth and logic. It takes longer but it is the only way to build a safe and inclusive community.